🕑 5 min read
Google Quantum AI reveals that cracking Bitcoin’s cryptography requires 20x fewer resources than previously estimated – and a privacy upgrade made things worse.
Google’s Quantum AI team just dropped a bombshell on the crypto world: quantum computing could crack Bitcoin’s cryptography with fewer than 500,000 physical qubits. That’s a 20-fold reduction from previous estimates that put the number in the millions.
The kicker? Bitcoin’s Taproot upgrade – the one celebrated for improving privacy and efficiency – actually widens the pool of vulnerable wallets by exposing public keys on the blockchain by default.
At today’s price of $66,369, approximately 6.9 million BTC sit in addresses with exposed public keys. That’s $458 billion.
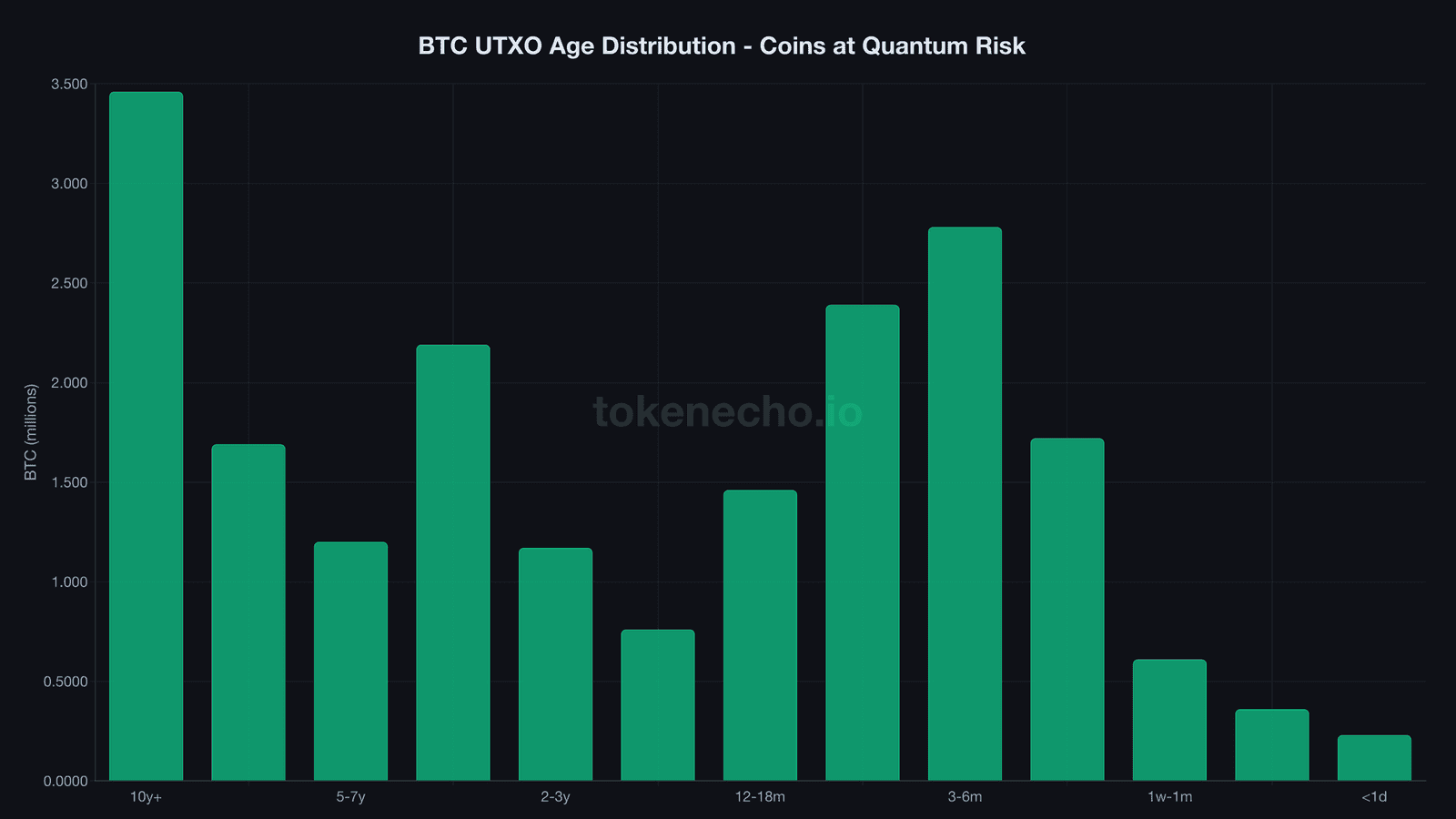
6.9 Million BTC Exposed – And That Number Just Got 680x Bigger
Previous industry estimates from CoinShares pegged quantum-vulnerable Bitcoin at roughly 10,200 BTC. Google’s research blows that number apart – 6.9 million coins, or about one-third of the entire circulating supply of 20 million BTC.
Where does that figure come from?
About 1.7 million BTC sit in ancient Pay-to-Public-Key (P2PK) addresses from Bitcoin’s earliest days. These are the Satoshi-era coins, the ones mined before anyone worried about quantum threats. Their public keys have been visible on the blockchain since the day they were created.
But the real surprise is the remaining 5.2 million. These belong to addresses where the owner reused a public key across multiple transactions – a practice that strips away the hashing protection that normally shields keys from prying quantum eyes.
“We employed a zero-knowledge proof to demonstrate our findings without revealing actual attack methods,” said Ryan Babbush, Director of Research at Google Quantum AI, describing the team’s responsible disclosure approach.
His co-author Hartmut Neven, VP of Engineering at Google Quantum AI, outlined two attack implementations: one requiring fewer than 1,200 logical qubits with 90 million Toffoli gates, and another needing fewer than 1,450 logical qubits with 70 million gates. Both run in minutes, not hours.
Nine Minutes to Steal a Bitcoin Transaction
The scariest part of Google’s paper isn’t the long-term threat. It’s the short-term one.
A sufficiently powerful quantum computer could hijack an in-flight Bitcoin transaction in approximately nine minutes. Bitcoin’s average block confirmation takes ten. Do the math – that’s a 41% chance of beating the network to the punch.
Picture it: you broadcast a transaction, and a quantum attacker derives your private key from the exposed public key before a miner confirms the block. They redirect your coins. Transaction complete, funds gone.
Nobody can do this today. Not even close. But the gap between “theoretically possible” and “practically executable” just shrank by a factor of 20.
Taproot Was Supposed to Improve Bitcoin. It Widened the Attack Surface Instead
This is the contradiction nobody saw coming.
When Bitcoin activated Taproot in November 2021, it was the biggest protocol upgrade in four years. Schnorr signatures replaced the old ECDSA scheme for Taproot outputs, making multisig transactions cheaper and more private. The crypto community celebrated.
What they didn’t discuss much: Pay-to-Taproot (P2TR) addresses expose the public key directly on the blockchain by default. Legacy Pay-to-Public-Key-Hash (P2PKH) addresses – the ones most wallets used before Taproot – concealed keys behind an additional SHA-256 hashing layer.
In other words, Taproot traded one form of security for another. And in a post-quantum world, that trade looks increasingly lopsided.
The irony cuts deep. An upgrade designed to make Bitcoin more efficient and private actually expanded the quantum attack surface. It’s like upgrading your front door lock while accidentally leaving a window open that didn’t exist before.
BIP-360 Exists. Nobody’s Implemented It.
Bitcoin developers aren’t blind to this problem. BIP-360, the first formal Bitcoin Improvement Proposal addressing quantum resistance, introduces Pay-to-Merkle-Root (P2MR) – a new address format that removes Taproot’s key path spending option entirely and forces all transactions through script paths that minimize elliptic curve exposure.
On paper, it’s elegant. In practice, it’s stuck in draft.
No timeline has been set for activation. No migration has begun. And NIST-standardized post-quantum signature schemes like CRYSTALS-Dilithium and SPHINCS+ produce signatures that are roughly 200 times larger than current elliptic curve ones. That means bigger transactions, heavier blocks, higher fees, and potential denial-of-service vectors.
Bitcoin’s decentralized governance – the thing that makes it resilient – also makes it glacially slow at adopting protocol changes. The Taproot activation itself took years of debate. A quantum-resistant migration would be orders of magnitude more complex.
Google’s internal deadline for migrating its own authentication services to post-quantum cryptography? 2029. That’s three years from now.
The Market Doesn’t Care (Yet)
While Google’s researchers warn about a $458 billion vulnerability, Bitcoin traders seem focused on more immediate concerns. BTC closed its worst quarter since FTX at $66,878, down 47% from its all-time high of $126,080.
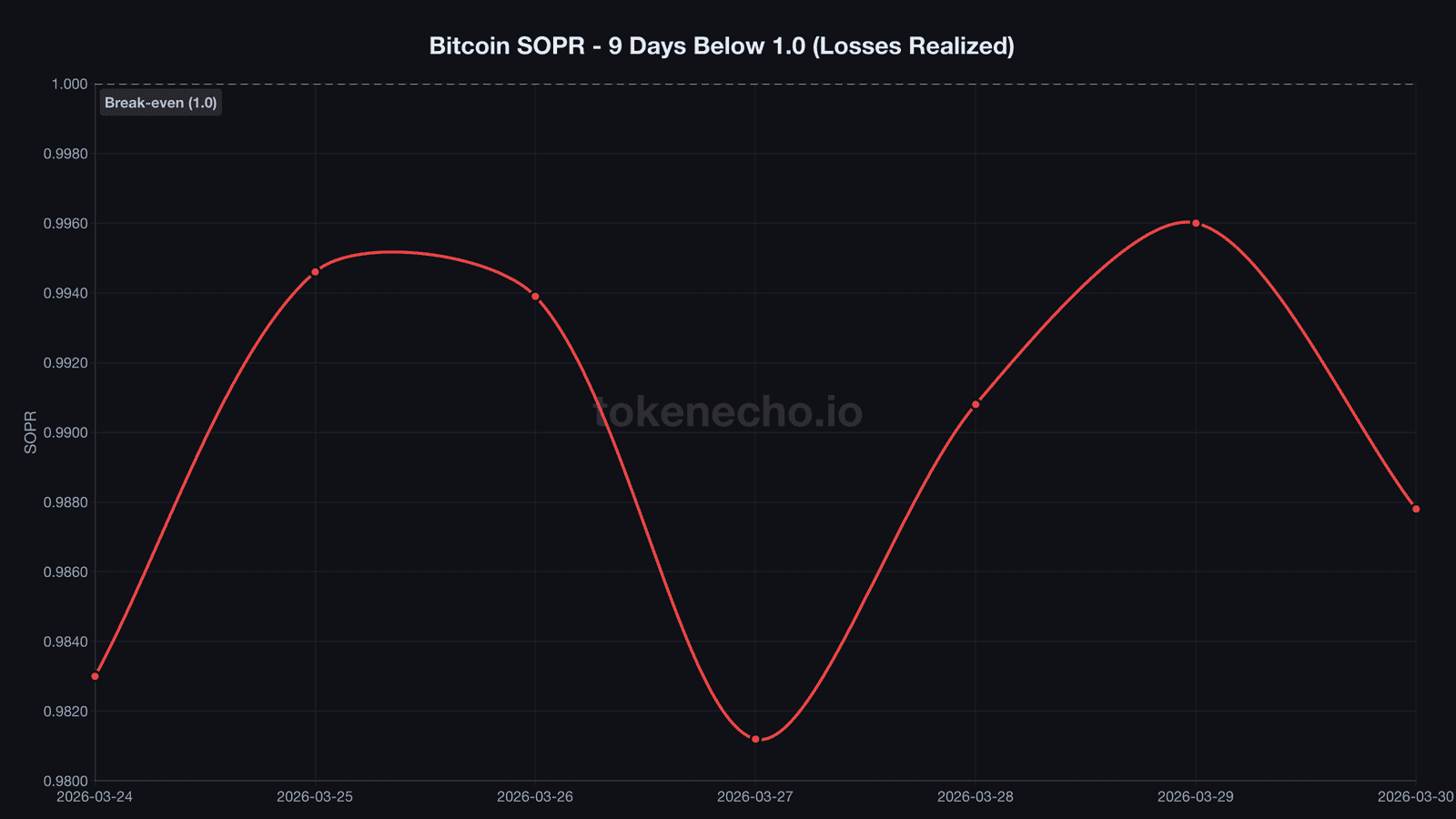
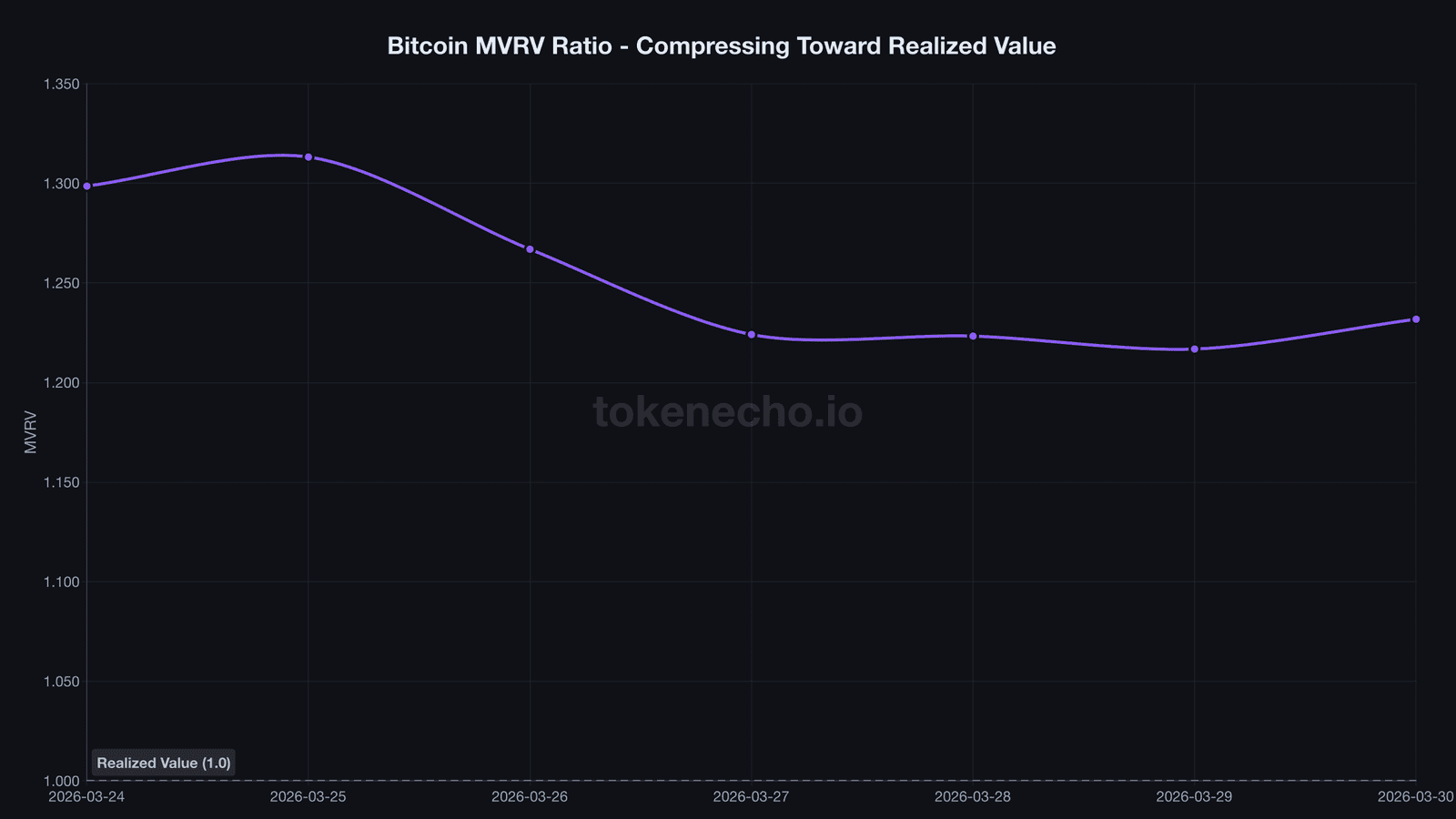
SOPR has remained below 1.0 for nine consecutive days – every coin being sold is sold at a loss. MVRV sits at 1.23, compressed against realized value. NUPL hovers at 0.188, flirting with the capitulation zone.
And yet, amid all this, whales keep buying the dip against a 4.5% risk-free bond yield. Exchange reserves have swelled by over 8,600 BTC in the past six days as some holders capitulate while larger players absorb the selling pressure.
The quantum threat is real, but it’s a 2029 problem competing for attention against a 2026 market that can’t seem to find a floor.
What Can Bitcoin Holders Actually Do?
For now? Not much – and that’s kind of the point.
Avoid reusing addresses. That’s the simplest step. Every time you receive BTC to a fresh address and don’t reuse it, your public key stays hidden behind a hash until you spend from that address.
Avoid P2PK-format coins if you’re somehow still holding them (you’re probably not – these are mostly ancient wallets).
Watch BIP-360’s progress. When – not if – Bitcoin begins its post-quantum migration, early movers who shift coins to quantum-resistant addresses will protect themselves before the rush begins.
And keep an eye on Google’s own 2029 deadline. If Google’s quantum hardware team believes they need post-quantum protection within three years, the clock is ticking for everyone using the same underlying cryptography.
Bitcoin’s 20 million circulating coins are worth $1.33 trillion. One-third of them just got flagged as vulnerable by the company building the world’s most advanced quantum computer.
This is not financial advice. DYOR. Data as of March 31, 2026.

Leave a Reply